Category: Cybersecurity
-
Extended Detection and Response platforms have become the backbone of modern security operations. They pull together data from endpoints, networks, and cloud environments to give security teams better visibility and faster response times. But here’s the uncomfortable truth: even the best XDR platforms still struggle with one critical problem. They’re fundamentally reactive. You’re monitoring, analyzing, and responding to threats that have already…
-
XRP has landed in 5th place by market capitalization, with a value of $114.53BN at press time, losing its position to BNB (Binance Coin), the native crypto of the Binance exchange ecosystem. This platform is known as the leading online crypto exchange around, where you can track crypto prices, invest, keep up with the news,…
-
Trading platforms feel exciting because everything moves quickly and opportunities seem endless. That same speed also creates perfect conditions for scams to thrive unnoticed. Globally, the online trading platform market, as of 2023, is valued at over $9.50 billion. With millions across the world trading online, these platform users are at constant risk of being…
-
If your site gets flagged for malware, users bounce. If your checkout page looks suspicious, people abandon carts. If your login is misconfigured, accounts get abused. Interestingly enough, all this often starts with something simple. Like an outdated plugin, a weak TLS setup, or a malicious script that gets injected into a page you didn’t…
-
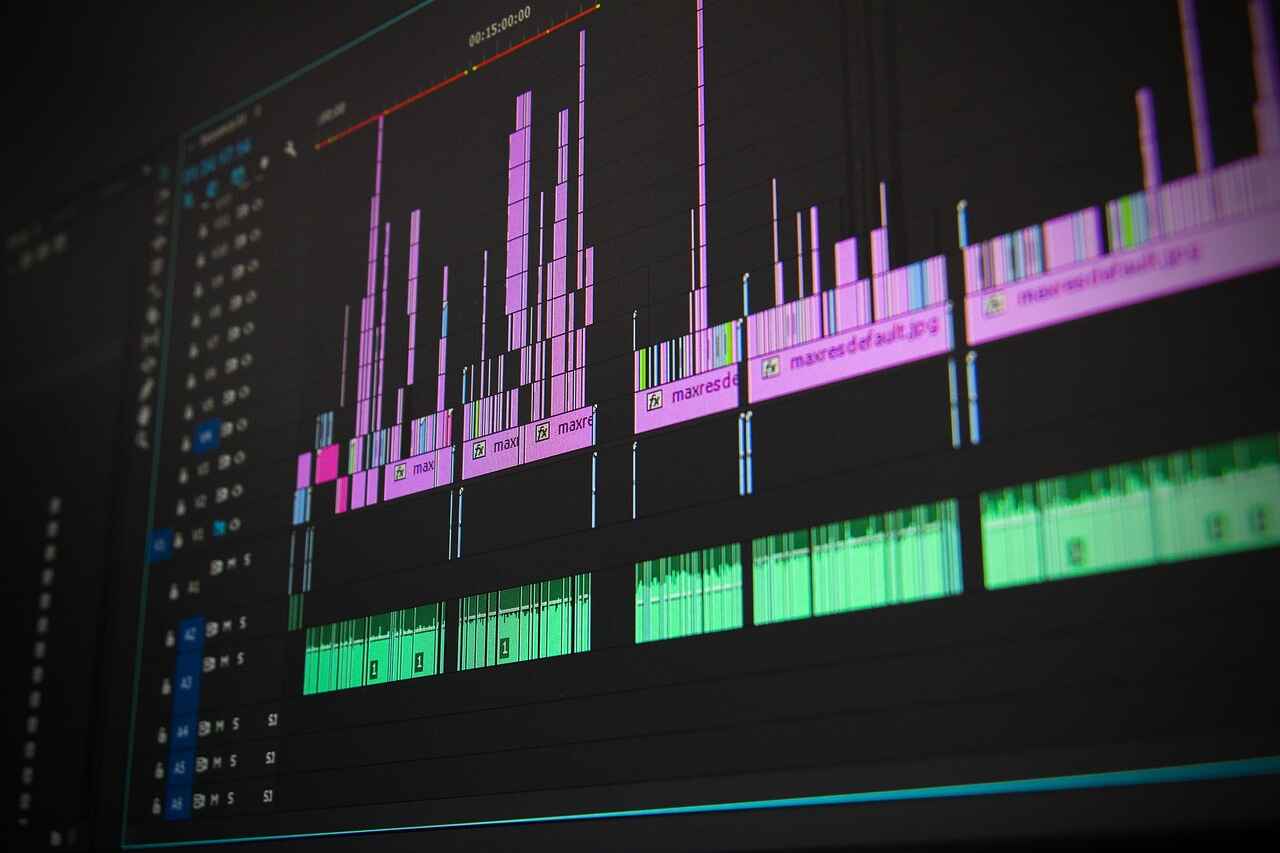
Remote creative teams have become a structural norm in design, media, software, marketing, architecture and countless hybrid fields where ideas travel faster than products. But this fast flow of digital work comes with serious consequences. Every shared file, every brainstorming platform, every exported prototype and every cloud-stored storyboard increases the risk of exposure. If you…
-
For many business owners, having a website that is secure is often seen as more of a technical issue rather than one that actually drives growth. Of course, as is the way with most things, if there is security, there is the chance for it to have a role in helping your business to grow.…
-
Understanding SPF Flattener: Definition and Purpose Sender Policy Framework (SPF) is a standard email authentication method that allows domain owners to specify which email servers are permitted to send messages on behalf of their domain. This is achieved by publishing an SPF record in the DNS, listing all allowable IP addresses and third-party email services via a, mx, include, and redirect terms. However, as…
-
As we enter 2026, deepfake technology has advanced at a pace few predicted. What began as a gap AI experiment has evolved into a powerful, easy-to-use device able to manipulate audio, images, and video at near-best accuracy. While this innovation has benefits in amusement and creative industries, the darker side of deepfakes poses sizeable risks…
-
Attackers constantly search for opportunities to capture passwords because these credentials open direct paths to valuable accounts and systems. Their methods range from technical tricks to highly convincing deception, and each approach aims to exploit gaps in attention or weak points in security setups. Strong awareness helps you recognize what these attempts look like before…
-
Digital workflows support everyday tasks across modern organizations, and their efficiency often depends on how securely information moves through each step. Teams rely on connected platforms, shared documents, and automated processes, which means any weak point can affect the entire system. A few practical actions can strengthen protection without slowing work. Simple improvements help teams…